This post brought to you by Carbonite. The content and opinions expressed below are that of No Passive Income.
Nowadays, the fight of data security against cybercrime is one of the biggest challenges for the small businesses.
Analysts have noted a growing number of attacks on the server side, with increasingly sophisticated threats that use encryption to mask malicious activity.
According to the latest Cisco 2016 Annual Security Report, the attackers commandeering legitimate infrastructure and reaping millions in profit, while businesses are struggling to detect and combat threats.
The defender confidence in their ability to detect, defend, and recover from cyber attacks is falling, while regulators and investors are seeking more visibility into organization’s cyber risks.
Truth is that businesses fail all the time, but data should never be one of their failures. These small business stories prove that it’s possible to turn fails into sales.
Almost half of businesses (47%) declare that fear of losing data is something that keeps them up at night, and there’s good reason, because it’s likely to happen!
In 2015, 22% of companies have experienced data loss, with nearly 50% recovering less than half of their data. This is really costly for businesses.
According to IDC (International Data Corporation: The Growth Opportunity for SMB Cloud and Hybrid Business Continuity Sponsored by: Carbonite, by Raymond Boggs, Christopher Chute & Laura DuBois; April 2015), 80% of small and midsize businesses have experienced downtime in the past, with related costs ranging from $82,000 to $250,000 per event.
The researchers observed that with some simple but important measures companies could greatly improve the safety of their data.
Here are some practices to be followed.
Table of Contents
1. Establish a Data Security Plan
Start with a plan outlining the actions to be taken in relation to the different security breach scenarios to prevent data loss.
Include policies which establish whether and how employees can access various data. This should serve as a real manual of safety rules for all the staff and what planned should strictly be applied.
For example, if a rule states that the personal devices used by employees should be password protected, do not make exceptions for anyone, not even for the boss.
Finally, the plan should be a document that changes and evolves in relation of how the business grows and expands.
2. Educate and Train Employees
Educate employees about the security risks and provide regular training on topics like the use of passwords, how to deal with incoming unsolicited emails or data backup.
As you can see from the following image (taken from this research):
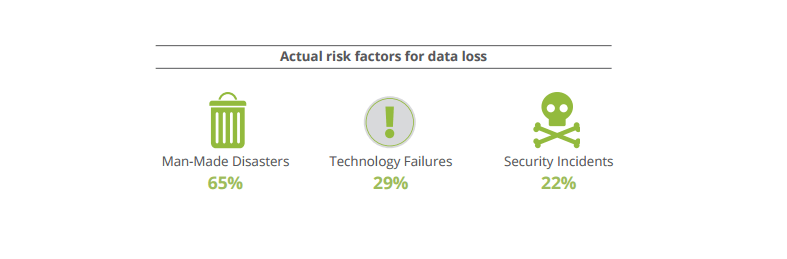
Most of the actual risk factors for data loss are man-made disasters.
Make sure that employees always know who to address if an unusual or unexpected problem comes during the course of their digital workday.
And don’t forget natural disasters. They may not seem a frequent situation, but they are actually a huge potential for data disruption.
Make sure to have a disaster recovery strategy!
3. Prepare a Disaster Recovery Plan
Disaster recovery is the ability to come back to standard operations in the event of a disaster.
Think of a disaster not just as a flood destroying your offices, but also as an employee who accidentally throws some coffee on his laptop.
It may sound scary, but a disaster recovery is really important for your business. Here are some steps you can follow to set up a strategy:
- assemble a dedicated team;
- decide which devices you want to back up;
- set the data you want to back up;
- decide where you will store the data;
- set the amount of time to get your business back and running;
- write down your plan and test the strategies.
4. Establish a Data Storage Policy
Create and follow a policy for storing business information outlining what data should be stored and which data can be erased.
Make sure to just store essential data, because one mole of stored but not necessary data only increases the risk of security.
5. Include the Protection of Mobile Devices
The devices connected to the Internet through the company network include server, desktop and notebook PCs but also (and now increasingly) tablets and smartphones. And as mobile connectivity becomes easier, data becomes even more vulnerable when they are moving.
Most companies allow employees to download non-controlled applications on their devices, thus creating a highway for hackers to steal corporate data. Do not allow mobile devices to access the network unless they comply with corporate security policies you define. Also, be sure that the threat management incumbent on mobile devices is an integral part of the overall company security solution to increase data protection.
Other than setting a strong password, here are some other practical suggestions to increase the protection of mobile devices in your business:
- remote wipe: thanks to this feature, a device connected to the Internet can be located right away, if it’s stolen or misplaced. You will be able to wipe the data remotely, then;
- updates: be sure to stay updated on those alerts. It’s suggested to set to automatically download them;
- antivirus: use a premium software, not a free one. Make your purchases from an authorized and official app store, rather than from third party sites. Anti-virus protection is a must, especially for Android devices;
- no jailbreaking: pay attention to not install software that breaks a device’s closed ecosystem, as it may open a gate for malware to get in. Remember, malwares can be anywhere, including an app that employees download.
6. An Approach to Safety at All Levels
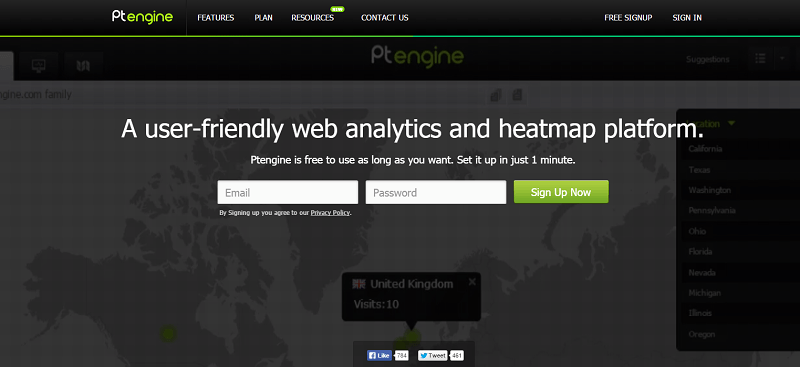
Dealing with data has never been more challenging for small businesses. It’s important to keep up with digital innovation and get a protection that stay constantly updated.
Choose a package of solutions that includes defense against both external threats (viruses, intrusions, malware attacks) but also to the company’s internal threats (improper use of IT tools by employees or fraudulent subtraction of data). And, above all, trust in a security technology vendor which must be simple to install, manage and maintain.
You must always be able to easily add new users and devices, together with making changes and updates in a few minutes, including the option to manage all your security tools from a single console.
Remember, a product based on the cloud like the one offered by Carbonite enables access anytime, anywhere. Claim your 30 day free trial and protect your data today.
What do you think?
Are you running an online business?
What are you doing to increase data protection and ensure your business security?
Please share your experience in the comments below, thanks!








Hey Erik,
The starting point for any business must be understanding what data is business-critical or sensitive. We must identify how it’s used and where it’s stored.
Everyone in our business must understand company security policy and know why it’s important. Education doesn’t need to be expensive, it can be integrated easily into the staff-induction process, and we could consider six-monthly refreshers to bring existing employees up to speed with any changes – including threats of which they should be aware. Education and communication are just as important as tools against cyber-crime as the computer technology which we use to defend our data.
An integral part of any small-business IT security strategy is a formal document that goes into proper detail and is then kept updated, rather than stuffed in a drawer and forgotten about. It may sound tedious, but we must plan not only how to protect our data and resources, but also what to do in the event that things go wrong.
Even when we have a security policy written up and implemented, the staff educated, the data encrypted and the devices under control, we can’t afford to rest on our laurels and assume we’re now secure. IT security is a dynamic, ever-changing landscape, and securing our data is our responsibility.
With best wishes,
Amar kumar
Hi! Erik,
In my opinion, you need to put up a strong firewall In order to have a properly protected network, “firewalls are a must,” Cloutier says. A firewall protects your network by controlling internet traffic coming into and flowing out of your business. They’re pretty standard across the board
Thanks, Erik,
This article is vital for all the business owner. Though we are very secure and safeguarding all our work data but because of some slight sensitive issue, we will inevitably face this critical point. Though the tips you have provided is also essential to maintain our data, other than that every employee must know their company security policy details its very mandatory. And the firewalls protect our network but instead along with this the above steps is also very very necessary, to maintain our standard and protect our business
Hey Erik,
I have recently faced this issue. My data was lost because of an unusual virus. It’s really hard to recover the whole data again.
It’s important to improve the security of your business. People are out there with the weapons to hit you directly.
I have come across an article last week stating that 70% of the websites are getting hacked every year. I mean it’s really scary.
I am sure, Carbonite can provide a better solution.
Thanks for sharing the info.
~Ravi
I think it is important to properly protect your company. Ensuring that your employees use secure passwords, keeping data stored or backed up in the cloud, using virus protection, and having staff members on hand in case there is an emergency. Great information, thanks for sharing!
This is a great list of things a business owner can do to make sure their data stays secure. Having a backup plan and training employees on safety has to be a top priority.
Data tends to be spread around, trapped in various silos. The latest wave of BI tools is attempting to remove the barriers between those silos so that a holistic picture is formed based on multiple data sources. This provides much more accurate forecasts.
These are great tips for securing business data! Losing valuable data/files can be devastating, and these are great ways for avoiding such situation! Thanks for sharing this!
These are awesome tips. Being able to identify security threats or breaches in your online security is one of the most important abilities for companies to have.